Its been quite a while I blogged. However during this big pause I learnt one thing about myself. I don’t publish unless I’m convinced information which I’m posting is not found or neatly explained. I have been always confused on persistent desktops, stateful desktops, stateless desktops, Full cloned, linked clone. I have only heard of linked clone, other terms are interchangeably used. This is post is aimed at clarifying these doubts.
Pools are basically collections of desktops. These desktop are either pre-created or can be created on the fly or can be created as demand increases.
Why we create pools?
Pool is like a group policy. If you define it once and it applies to group of users and computers. Similarly in pools you can defined various settings to control deployment of desktops, logoff action, provisioning style sysprep/quickprep.
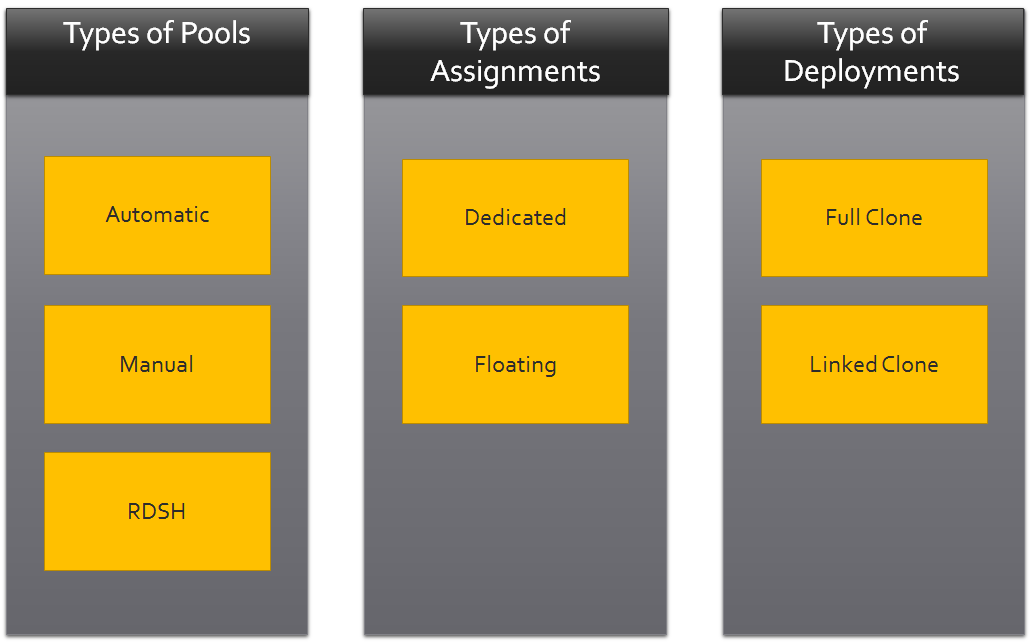
Types of Pools
Automatic Pool
Desktops are automatically created. You can specify total number of virtual machines you wish pool to provision at any given time. With automatic pool you also have option to keep minimum number of VM to Spare for new users. This will allow you to control how frequently VMs should be provisioned, there by controlling load on the view composer/vCenter servers. Setting also ensures desktops are available for immediate use. Please note horizon view licenses are based on current users. Once you know the number of concurrent users, you can designed this parameter accordingly. If you are purchasing 1000 concurrent user licenses, then you should never put more than 1000 as maximum number of VM per pool.
Manual Pool
Manual is used when Desktop VM is already provisioned and available in vcenter. Or it is not managed by vCenter (e.g. Hyper-V, SCVMM) or it is physical desktop. Very limited use case.
RDSH Pool
It is terminal service now renamed by Microsoft as Remote Desktop Services (RDS).Primarily used to publish session based desktops and applications. However in RDSH pool, You can only create a session based desktops for users. Remember this is not pool of desktops. User can log into RDSH simultaneously. RDSH based desktop pools only supports Windows Based desktops. Again, very limited use case for desktops. In fact RDSH real power is to publish applications on RDSH servers and make it accessible from any device.
Decision on which one to use
Simplest way to select the type of pool is to find if you are using only view based VMs? If yes, answer is automated pool.
Are you going to use some 3rd party desktop management software and User profile management software? If answer is Yes, think of RDSH based pool.
Note: RDSH based pool do not support persona management. So decision is primarily around user profile management and operations. RDSH based desktops pools use case is very limited. Use cases which RDSH based desktop can solve are already covered and over lapping with Automated pool
1. Roaming profile management (Automated Pool)
2. Image management (Automated Pool)
3. Users don’t want to buy software licenses per desktop (RDSH Based Desktop)
e.g. MS Office, Windows OS license and other software products which support CAL types.
4. User must get same desktop every time he logs in (Automated Pool)
5. User need custom application installed on his desktop (Automated Pool)
# [4] RDSH you don’t have floating desktops or dedicated desktop pools.
What else users work profile would be? It is major driving factor to choose Automated over RDSH Pool.
In next post we discuss Types of Assignments and Types of Deployments how they further impact the pool selection type.